Crypto bridges enable cross-chain asset transfer and data sharing, expanding liquidity and multi-chain usability. Designs range from trustless and validator-based systems to wrapped assets, each with distinct security guarantees and capital efficiency. Assessing bridges requires weighing security models, liquidity depth, and vulnerability vectors such as finality gaps and re-entrancy. Practical selection hinges on guarantees, audits, governance, latency, and fees. The tradeoffs and evolving mitigations present a continued point of examination for robust interoperability.
What Crypto Bridges Do and Why They Matter
Crypto bridges enable interoperability between disparate blockchain networks by transferring assets and data across chains. They facilitate cross chain liquidity, enabling users to move value without centralized intermediaries. Bridges security remains paramount, as vulnerabilities can undermine confidence.
Wrapped assets preserve underlying economics while expanding interoperability, yet introduce counterparty risk. Understanding mechanics, governance, and risk models clarifies why bridges matter for freedom and rapid, permissionless innovation.
How Bridge Designs Differ: Trustless, Validator-based, and Wrapped Assets
Bridge designs differ fundamentally in how they achieve cross-chain interaction, balancing trust assumptions, security guarantees, and capital efficiency. The discussion centers on trustless design, validator based systems, and wrapped assets, each shaping cross chain messaging and asset transfer. Trustless designs minimize central authority but require robust cryptography. Validator based approaches rely on trusted nodes, while wrapped assets enable liquidity without direct custody, trading off complexity for interoperability.
Evaluating Risks: Security, Liquidity, and Attack Vectors
Evaluating risks in cross-chain bridges requires a structured assessment of security guarantees, liquidity dynamics, and plausible attack vectors.
The analysis isolates security pitfalls and evaluates liquidity dynamics under varying stress scenarios, including asset re-entrancy, cross-chain finality gaps, and validator incentives.
Findings emphasize formal verification, multi-party computation, and robust exit mechanisms to reduce exposure and preserve user freedom.
Choosing the Right Bridge: Criteria and Practical Use Tips
Given the prior scrutiny of security, liquidity, and attack vectors, selecting an appropriate cross-chain bridge requires a structured framework that weighs guarantees, liquidity depth, and exposure under stress.
The analysis favors bridges with transparent bridge security audits, robust incident response, and clear governance models.
Practical tips include validating cross-chain latency, fee structures, and governance models before deployment.
Frequently Asked Questions
How Do Bridges Impact User Privacy and Data Exposure?
Bridges can introduce privacy leakage through cross-chain metadata and observability; implementing data minimization reduces exposed information, while cryptographic methods and selective disclosure constrain data sharing, enabling users to pursue freedom with tighter controls and verifiable, minimal exposure.
What Fees and Costs Are Typically Associated With Bridges?
Bridge costs vary but typically include transaction fees, mint/burn fees, and validator or relayer gas. Additionally, bridge security and liquidity incentives influence spreads, volatility, and fees, impacting users’ total cost and capital efficiency in cross-chain transfers.
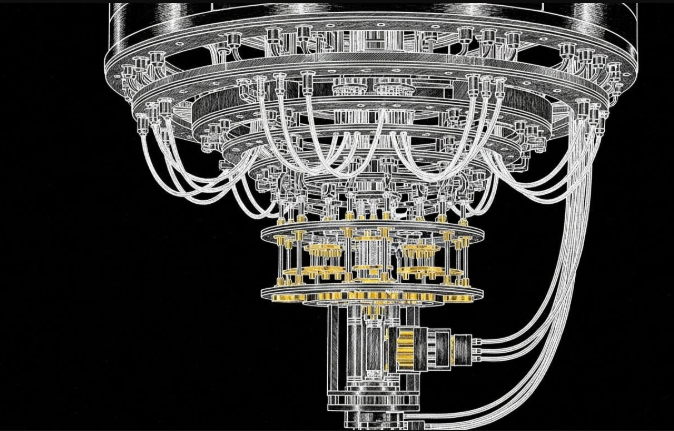
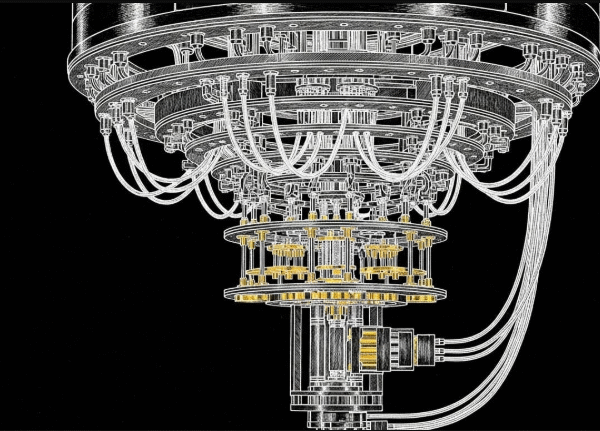
See also: Quantum Computing Basics Explained
Can Bridges Fail Silently or Cause Hidden Losses?
Yes. Bridges can fail silently or incur hidden losses due to complex cross-chain mechanics, governance quirks, and decommission risks, presenting silent outages, privacy exposure, and data-dependent weaknesses that demand rigorous, data-driven risk management and ongoing surveillance.
How Do Bridges Handle Cross-Chain Governance and Voting?
Bridges implement governance via multi-sig or on-chain voting contracts, enabling cross-chain voting and parameter updates; governance weight and security depend on trusted relays and bridge design, with transparent audits guiding implications for users seeking freedom.
What Happens if a Bridge Is Decommissioned or Paused?
Like Icarus cautions, a decommissioned bridge halts transfers; paused operations suspend access. The system records final states, preserves audit trails, and notifies users, while frozen liquidity and cross-chain vetoes constrain recovery and governance flexibility in decommissioned bridges.
Conclusion
Crypto bridges enable cross-chain asset mobility while distributing risk across designs. Trustless models maximize security through cryptographic guarantees but demand robust finality and uptime; validator-based bridges balance throughput with social consensus; wrapped assets trade custodial risk for liquidity. A practical bridge choice hinges on guarantees, liquidity depth, and audit rigor. Anticipated objection: bridges are inherently risky; while no system is risk-free, rigorous formal verification, multi-party security, and clear exit paths materially reduce attack surfaces and improve resilience.